How To Protect Volume Shadow Copy From Deletion
Volume Shadow Copy is a great and value add on to windows and can save data lost very fast and efficient . In the last years when virus and ransom virus appears the first think they do is to delete all of you shadow copies preventing you from fast restoring you lost files or encrypted files. Forcing you to pay or to use the backups you made to you file and data.
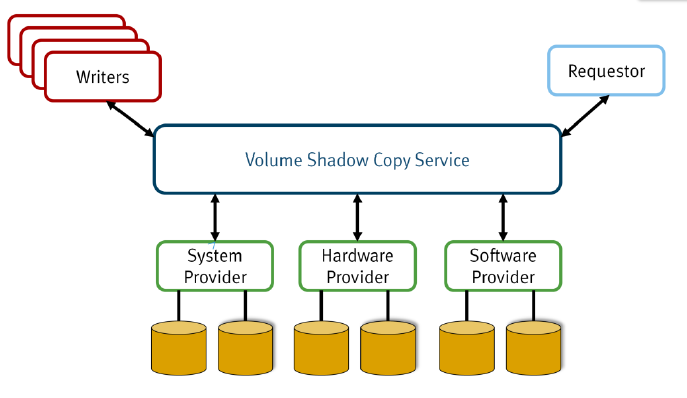
Volume shadow copy are created by the file system with the help of “Providers” accessing this feature with API option is a mean to create/delete Shadow Copies to a volume. Basically any one can write a code to manipulate the creation or deletion of Shadows with a code to connect to this API and manipulate this Shadows. more information from Microsoft here
A full explanation on how Volume Shadow Copy work can be found here :
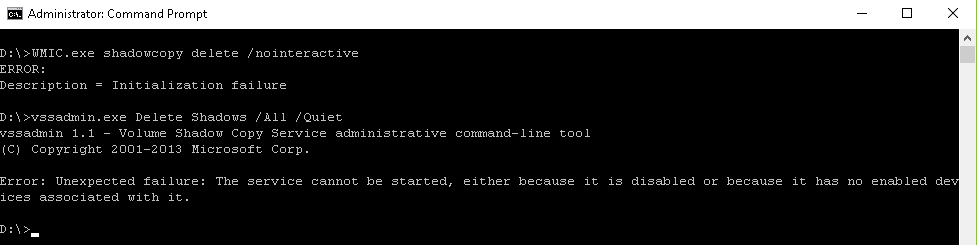
The Volume Shadow Copy is managed by the service VSS, So if we disable this service the API will not function. now most of the virus script just run this before corrpting the data (if the are lazy writing there own scripts to the API):
vssadmin.exe Delete Shadows /All /Quiet
Or
WMIC.exe shadowcopy delete /nointeractive
But what if the service will be down and disabled ?
The API will be blocked for changes and our shadows will Survive !
Here is a simple script to start and create Volume Shadow Copy For a partition & stop and disable the service for protection (in the example Drive C: and Drive D: ) .
sc config VSS start= Demand net start VSS WMIC shadowcopy call create Volume=C:\ WMIC shadowcopy call create Volume=D:\ net stop VSS sc config VSS start= disabled
Then you can save as BAT file and scheduler this script to run as many times you want to create shadows for protection, Needless to say that when the VSS service is not running you will not be able to access the “Configure Shadow Copies…”
Please take under consideration that is another program need to use shadow copy service it will fail unless you will execute service start …
Shadow Copy is no backup !!! please make proper backups to your data